When it comes to the violation of image rights of a person, you will most likely be considering three legal implications: (1) violation of right to privacy; (2) violation of right of publicity; and (3) copyright infringement. Click link to.. Read more

Image Rights and How They Apply in Nigeria: A Scenario from IP ABC
Climbing the Legal Career Ladder through Arbitration & ADR Practice: A Young Lawyer’s Perspective
by Rita Anwiri Chindah, ACIArb Introduction For most lawyers, going to court to represent clients is a thing of joy. Many legal practitioners believe that if you are not in litigation, you are not in legal practice. Indeed, both oral.. Read more
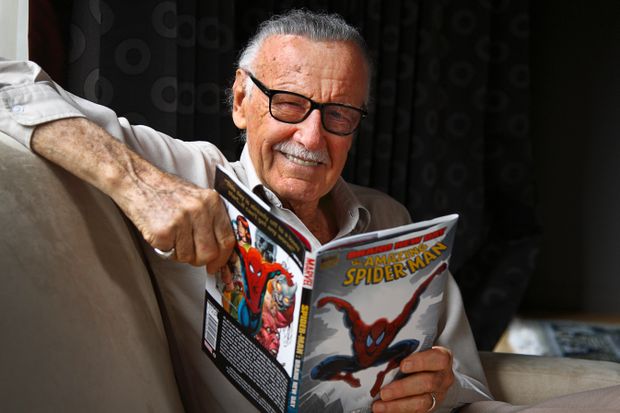
Stan Lee, legendary Marvel comic-book writer, passes on.
by Tobechukwu Ndunagwu Stan Lee (Stanley Martin Lieber) December 28, 1922–November 12, 2018 (95 years) was an American comic-book writer, editor, producer and publisher. Lee was key to Marvel’s expansion from a small division of a publishing house to a.. Read more

Day 30: Always prefer complicated passwords to simple ones.
Welcome to Cybersecurity in 31 Days. I’m Malan Faya, your host. Today is Day 30. To view previous posts, click here. Simple passwords are guessed in minutes by a password-cracker program. Always use complicated passwords. A password-cracker program can be used.. Read more
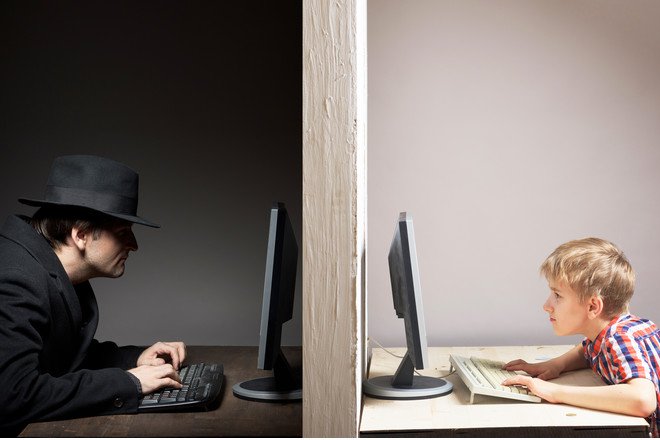
Day 29: Keep (your) kids away from danger online.
Welcome to Cybersecurity in 31 Days. I’m Malan Faya, your host. Today is Day 29. To view previous posts, click here. Kids may be exposed to danger online. Teach (your) kids what they can and can’t share over the Internet. Kids.. Read more

Day 28: Properly dispose of all sensitive hardcopy files.
Welcome to Cybersecurity in 31 Days. I’m Malan Faya, your host. Today is Day 28. To view previous posts, click here. Sensitive hardcopy files, if not properly disposed, can represent a significant security issue. A hardcopy file can be copied without.. Read more
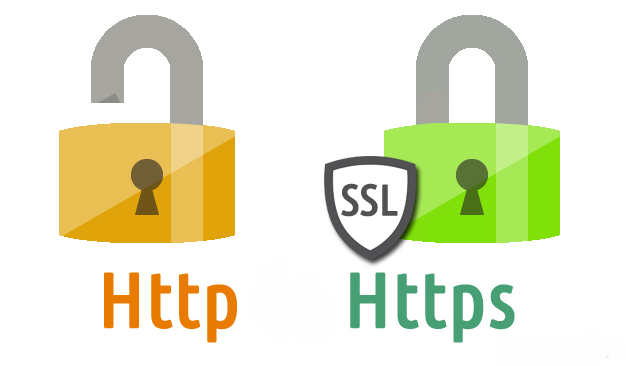
Day 27: Only send sensitive information through sites that use Secure Sockets Layer (SSL) or HTTPS sites.
Welcome to Cybersecurity in 31 Days. I’m Malan Faya, your host. Today is Day 27. To view previous posts, click here. For a safer web browsing experience, look for HTTPS in the web address before submitting sensitive information to a site… Read more

Day 26: Never open .exe files from your email.
Welcome to Cybersecurity in 31 Days. I’m Malan Faya, your host. Today is Day 26. To view previous posts, click here. Certain types of attachment are more dangerous than others. While viruses and malware can potentially be embedded in most types.. Read more

Day 25: Do not fall for scams by impersonators on social media.
Welcome to Cybersecurity in 31 Days. I’m Malan Faya, your host. Today is Day 25. To view previous posts, click here. Social media is now the haunting ground used by scammers in finding their victims. The most common social-media scams reported.. Read more

Day 24: Beware of SEO poisoning whenever you use a search engine.
Welcome to Cybersecurity in 31 Days. I’m Malan Faya, your host. Today is Day 24. To view previous posts, click here. Cybercriminals use search engine optimization (SEO) to trick you into visiting malware sites. SEO poisoning is an attack method that.. Read more

